If your average order value is high, your risk profile is high.
Luxury commerce brands are not selling commodity products. They are selling trust, exclusivity, and reputation. That means your infrastructure model cannot be an afterthought.
Managed Risks
Most managed storefront platforms are built for median merchants. They prioritize convenience over control, shared tenancy over isolation, and default workflows over strategic architecture. That can be acceptable for low-stakes catalogs. It is not acceptable when each order represents significant revenue and brand equity.
Solution
This post explains the infrastructure pattern behind a sovereign e-commerce stack: your own AWS organization, your own security boundary, your own deployment controls, and your own data ownership model.
True Ownership
The goal is to completely own the platform that owns your revenue.
What "Sovereign E-Commerce" Actually Means
Sovereign e-commerce does not mean "self-host everything manually."
It means:
- Your commerce platform runs in your cloud accounts, not a shared vendor tenancy.
- Your infrastructure is defined as code and auditable.
- Your production blast radius is intentionally constrained.
- Your data plane and control plane are separated.
- Your CI/CD identity model uses short-lived credentials, not static long-lived keys.
In practice, this yields better resilience, better governance, and better strategic flexibility as your business scales.
The Core Account Model
A clean sovereign architecture uses a dedicated account structure inside your AWS Organization:
- Main/Foundation Account: holds centralized Terraform state and deployment control roles.
- Production Account: runs the live commerce workloads.
- Non-Production Account: runs staging, performance testing, and release validation.
This isolates responsibilities while preserving a unified operational model.
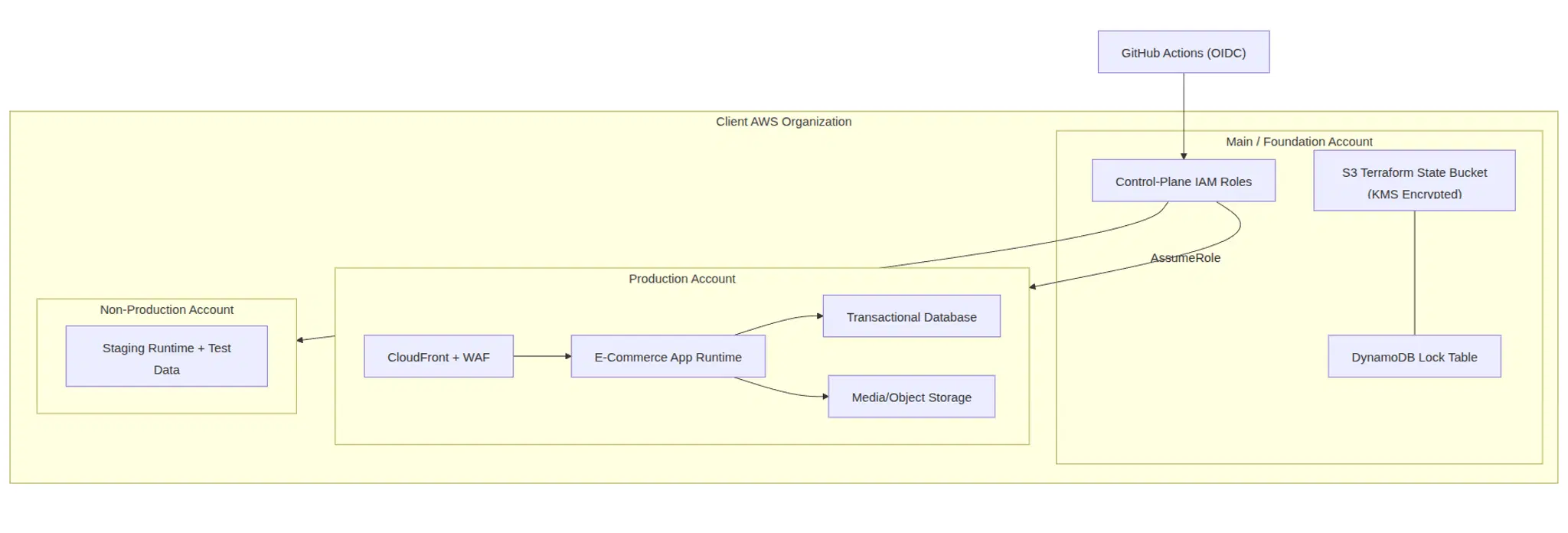
Conti Digital - Client AWS Organization Setup Diagram
Why Control Plane Separation Matters
In multi-environment Terraform, state is the source of truth for everything from networking to database topology. If state is weakly protected, the platform is weakly protected.
A hardened foundation separates:
- Control Plane: who can deploy, where they can deploy, and what state paths they can touch.
- Data Plane: application traffic, compute, storage, and customer data.
This split is foundational to enterprise reliability.
The IAM Trust Chain (Without Static Secrets)
A common anti-pattern is putting permanent AWS keys in CI variables. That creates a high-value secret with broad blast radius.
The sovereign pattern replaces this with GitHub OIDC:
- GitHub job requests a signed OIDC token.
- AWS validates token issuer, audience, and repository subject.
- AWS grants short-lived credentials to a scoped Main-account role.
- That role can assume only specific execution roles in specific workload accounts.
No static AWS access keys are required.
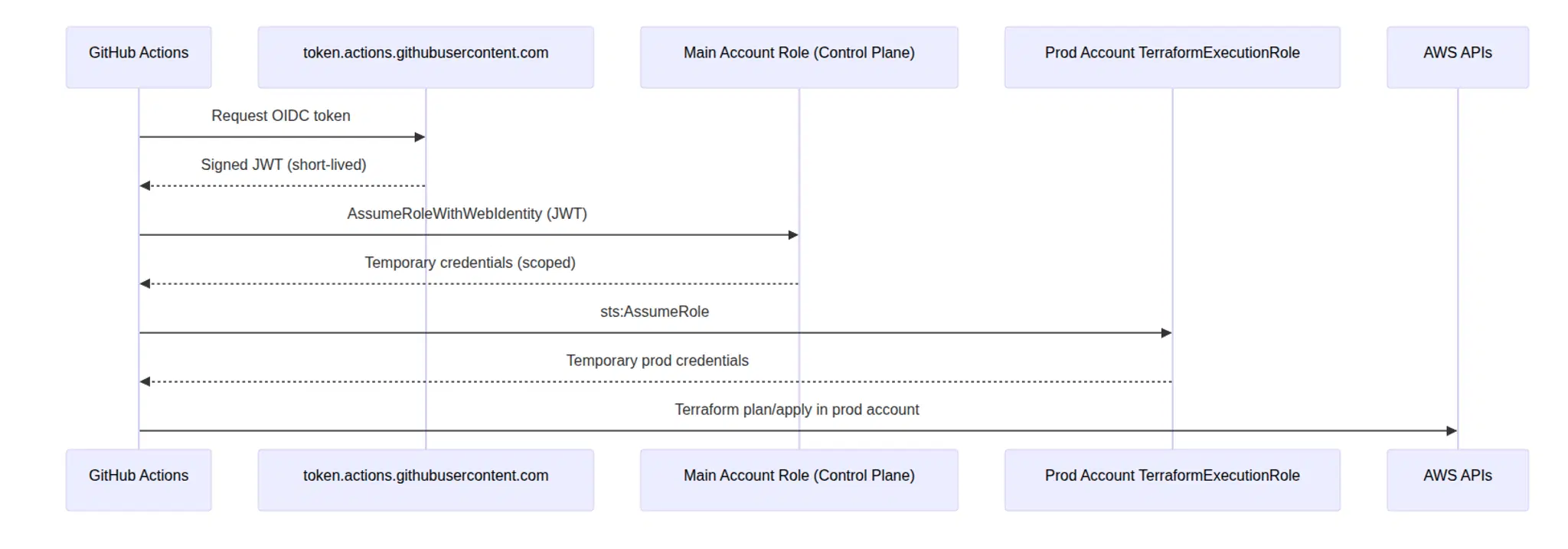
Conti Digital - Client AWS Infrastructure Deployment Control Diagram
State Security Is Non-Negotiable
A sovereign foundation must enforce state security at the policy layer, not by convention.
Key controls include:
- Versioned state bucket for full revision history.
- SSE-KMS encryption with customer-managed keys.
- Bucket policy denies for:
- non-TLS requests,
- unencrypted object writes,
- wrong KMS key writes.
- Public access block on bucket level.
- DynamoDB locking to prevent concurrent state corruption.
prevent_destroylifecycle controls on critical state resources.- Prefix-scoped IAM access so each workload can touch only its own state path.
The result is predictable governance with measurable blast-radius reduction.
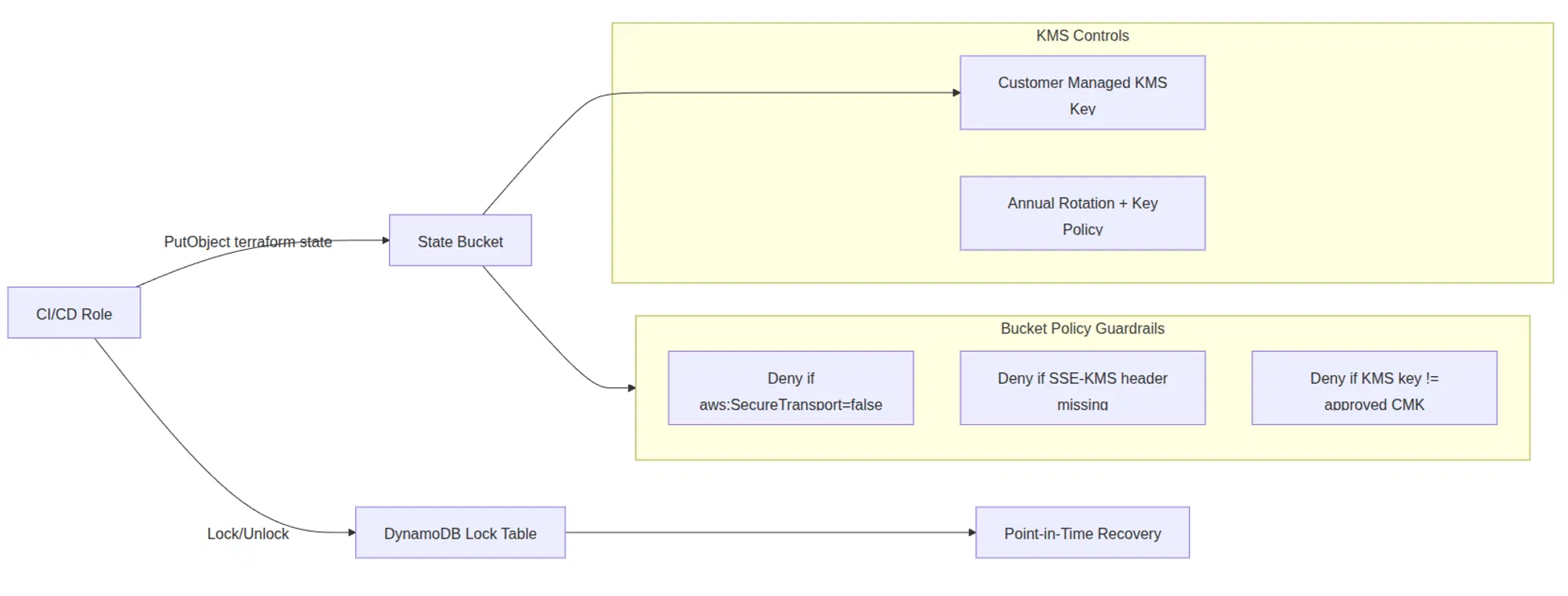
Conti Digital - Client AWS Infrastructure State Security Diagram
What This Enables for Luxury and High-Ticket Brands
For executive teams, this architecture maps directly to business outcomes:
- Brand protection: stronger isolation and explicit security baselines.
- Operational continuity: controlled deploys, lock-protected state, reversible changes.
- Strategic flexibility: you can evolve checkout, fulfillment, catalog, and personalization without platform lock-in.
- Data ownership: first-party control over sensitive commerce and customer data.
- Acquisition readiness: auditable infrastructure posture improves diligence outcomes.
Implementation Roadmap for Your Brand
A disciplined rollout should follow phases, not improvisation.
Phase 1: Foundation
- Establish account model and IAM boundary.
- Deploy Terraform state foundation (S3 + DynamoDB + KMS).
- Deploy OIDC-enabled control-plane roles.
Phase 2: Workload Landing Zone
- Create prod/non-prod execution roles.
- Implement VPC, edge, storage, and database baselines.
- Add monitoring, alerting, and backup controls.
Phase 3: Commerce Stack Deployment
- Deploy application services via Terraform.
- Integrate CDN, WAF, DNS, certificates, and media pipeline.
- Run security and performance validation.
Phase 4: Migration and Cutover
- Migrate data and media assets with rehearsed runbooks.
- Execute cutover with rollback checkpoints.
- Validate observability and post-launch SLOs.
Typical Deliverables in a Sovereign Engagement
When implemented correctly, you should receive:
- Production-grade Terraform repositories and modules.
- Documented IAM trust model and account topology.
- CI/CD workflows using OIDC and short-lived credentials.
- Environment-specific backend and provider patterns.
- Migration runbooks and incident playbooks.
- Operational handoff documentation for internal teams.
Who This Is For
This model is ideal for:
- Luxury brands with high average order value.
- Commerce teams planning aggressive growth or international expansion.
- Operators who need strict governance and long-term platform control.
- Founders preparing for diligence, investment, or strategic exit.
If your brand cannot afford platform fragility, this architecture is not optional. It is table stakes.
Final Point
You can outsource implementation. You cannot outsource ownership.
Sovereign infrastructure is not about complexity theater. It is about putting the legal, operational, and technical control of your commerce engine where it belongs: with your business.
If your current stack cannot guarantee that, it is time to rebuild on infrastructure you actually own.